Tesla Exploited at Pwn2Own 2023, Hackers Win $100,000 and Model 3 [Update]
Back in January the Pwn2Own security conference announced Tesla would be a sponsor again for 2023. The conference offers cash prizes for white hat hackers to demonstrate live exploits, allowing companies such as Tesla to learn more about beefing up their software and hardware security.
This year saw the addition of the Steam VM Escape category with multiple targets, since gaming is now widely available on Model S and Model X.
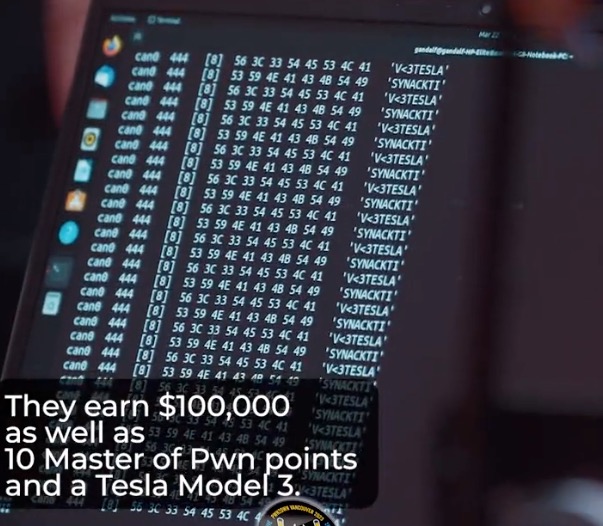
On day one of Pwn2Own held in Vancouver, BC, Canada, the Synacktiv team successfully executed a TOCTOU attack against the Tesla Energy Gateway. The team won $100,000, along with 10 Master of Pwn points and also a Tesla Model 3. While the Zero Day Initiative announced Synacktiv won a Tesla Model 3, a video shows them posing beside a Tesla Model S (update: check below).
CONFIRMED! @Synacktiv successfully executed a TOCTOU exploit against Tesla – Gateway. They earn $100,000 as well as 10 Master of Pwn points and this Tesla Model 3. #Pwn2Own #P2OVancouver pic.twitter.com/W61NasJPAl
— Zero Day Initiative (@thezdi) March 22, 2023
A TOCTOU (Time of Check to Time of Use) attack, also known as a race condition attack, is a type of cybersecurity vulnerability that occurs when a system’s state changes between the time a resource is checked (time of check) and the time the resource is used (time of use). This attack exploits the small time window between these two actions, allowing an attacker to gain unauthorized access or modify the resource during that brief period.
Hackers can win up to $600,000 for hacking a Tesla and win the car itself too. The Model 3 and Model S were on hand to be hacked. Last year a Model 3 was available as a target and it returns this year (Intel or Ryzen-based), while in 2023 a Model S is also available (Ryzen-based).
Last year, the Synacktiv team also exploited a Model 3 earning $75,000 as well at Pwn2Own, but the hack wasn’t complex enough to win the car.
Update March 24, 2023: Synacktiv clarified to Tesla North they did win a Model 3, but posed for a picture beside the Model S because it was there.
Want to see more of our stories on Google?

P.S. — Buying a new Tesla? Click here to save $1,000 USD, while supporting independent news.
Help support us by shopping on Amazon here.
Links in this post are affiliate links, so we earn a tiny commission at no charge to you. Thanks for supporting independent media!
